Hei,
I am trying to setup forwarding of all TCP traffic from Docker bridged network through SSH dynamic port forwarding (SOCKS5 proxy), but I feel myself a bit stuck. I some guidance and discussion around the task.
My use case is: We are a consultancy company that implements solutions based on a product where every process is running as Docker container. As a part of our work are are often connecting to customers services available over TCP in remote networks (database over JDBC is a typical example). We typically do not have a proper VPN access to the customers servers, but we can always rely on having SSH connection to customers server (this means being able to use dynamic port forwarding). We can’t presume that we can login as root user to remote servers, though.
We would really like to be able to run development environments on each persons machine insted of using one shared dev server on customers premises. That would means being able to access services over TCP in customers network from a machine that has SSH connection only. We would like this soltion to work independently of number and configuration of running containers.
Basically, we want to create a setup that would forward all TCP traffic from all Docker containers through SSH with dynamic port forwarding (SOCKS5 proxy) that is created by SSH session.
We would ideally prefer to also have a remote DNS resolution, but just traffic forwarding would be a wonderful starting point.
As for Docker service setup as for now we:
- Are using default Docker
bridgenetwork, and it is not possible for us to use Docker networking now - Are running the latest available versions of Docker service (we can rely on functions available in 1.11 now
- Are modifying host OSs
iptables
We are using Ubuntu 14.04 as OS on local server, but we can change to 16.04 as well.
My question is: What would be the best approach to solve it?
So far I have tried looking at:
-
Redsocks: It depends on getting
iptableson local server to work with bothREDSOCKSandDOCKER/DOCKER-ISOLATIONchains and I was not able to get it to work so far. Is it worth it going on looking into it? -
Redsocks as a container: Seems promising, but it seemed that port of the SSH session was open only as
127.0.0.1andlocalhost, and these hostnames were not available fromredsockscontainer. -
SSH VPN with tun/tap: Possible solution, but it presumes being able to login to remote servers as
rootand that is not always the case - Pipework: Seem promising, should I follow this way?
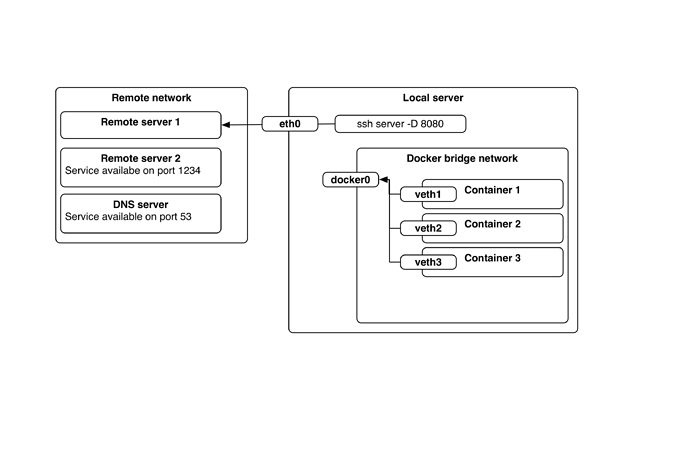
Here is the picture to illustrate current setup:
We want to get able to reach service that is available on
Remote server 2 over port 1234 over TCP from all containers (1, 2, 3 and other in case they would arrive).We would ideally prefer to get DNS resolved against remote DNS server as well.
Best regards,
Petr